Know what your dependencies
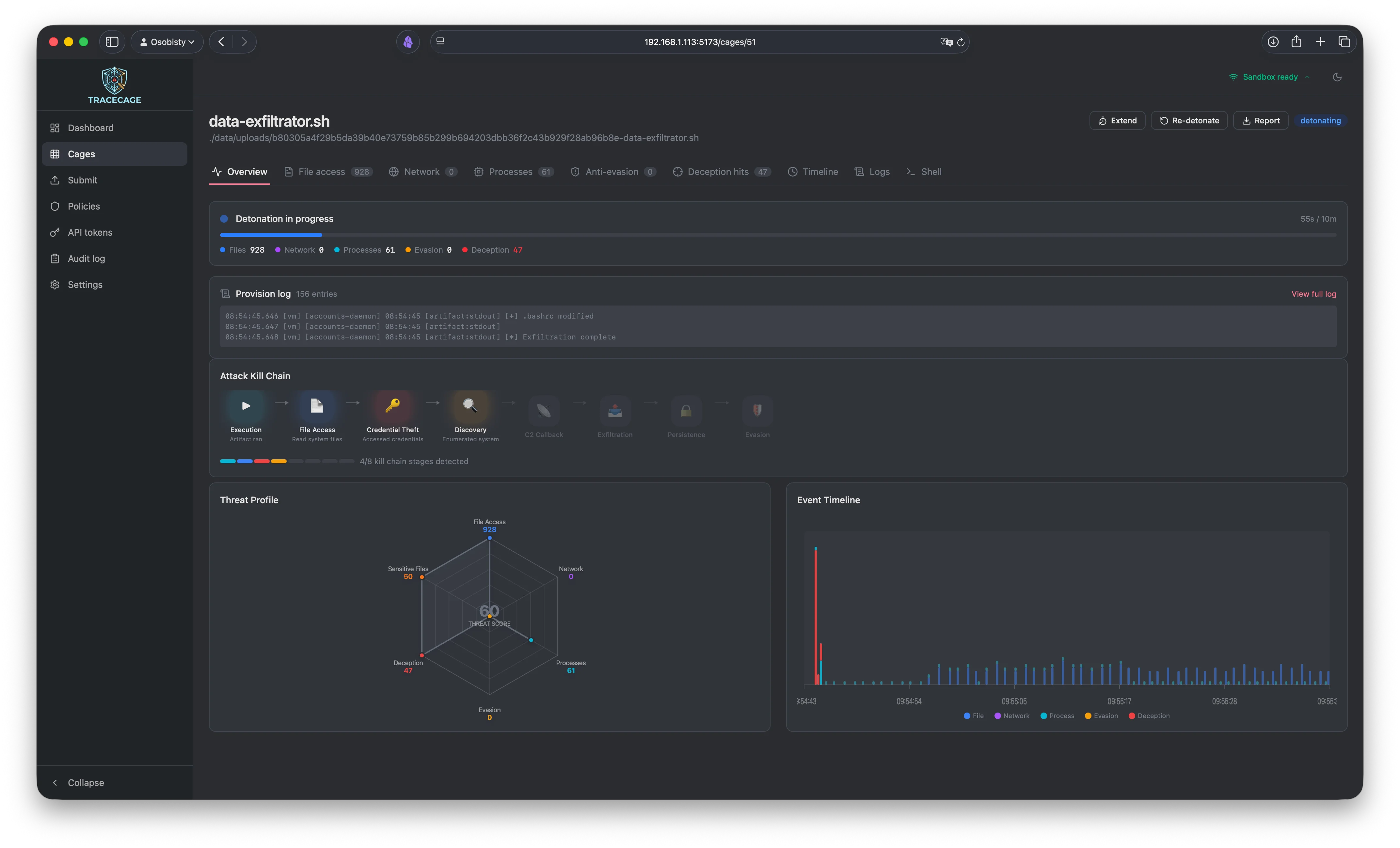
actually do at runtime
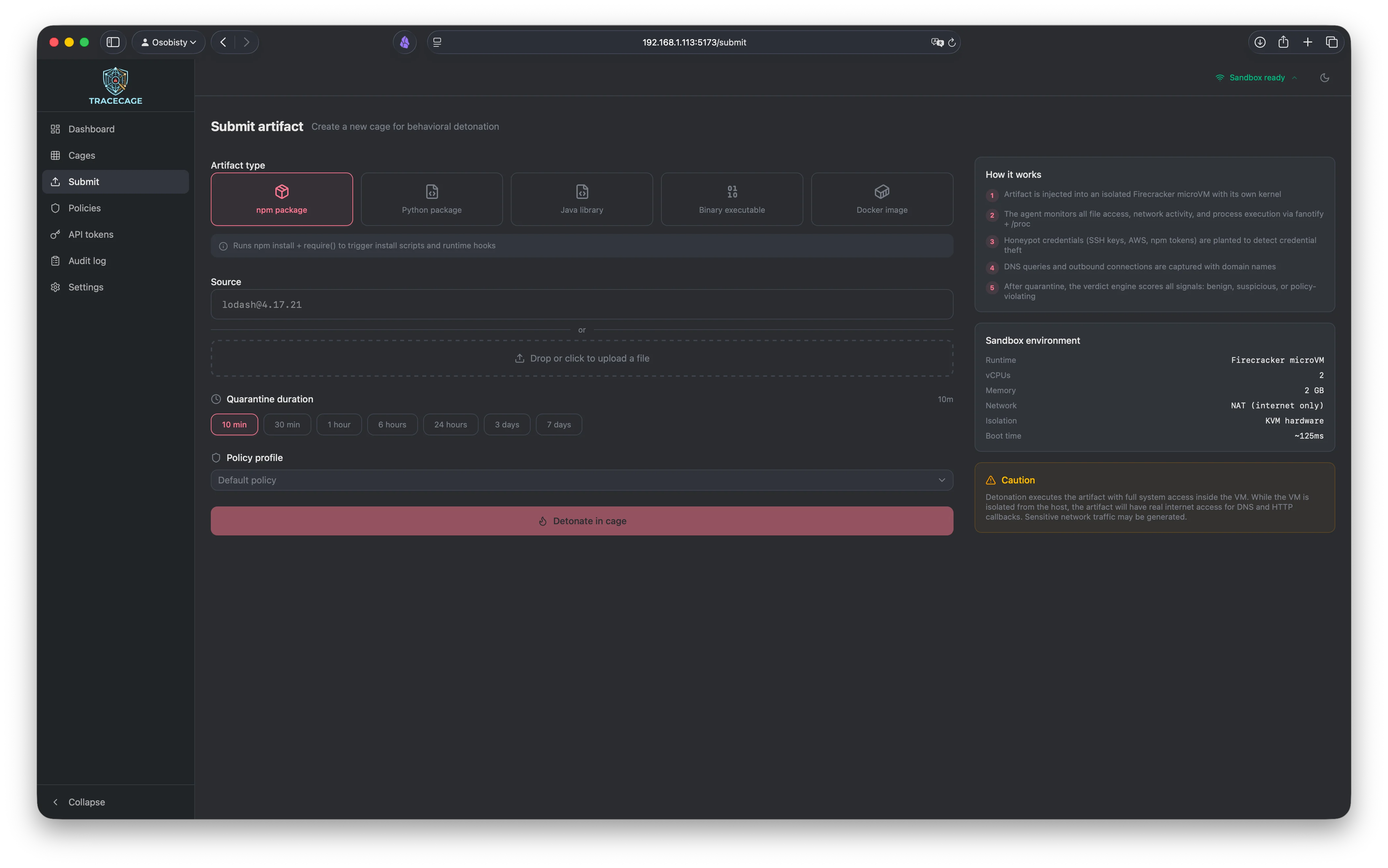
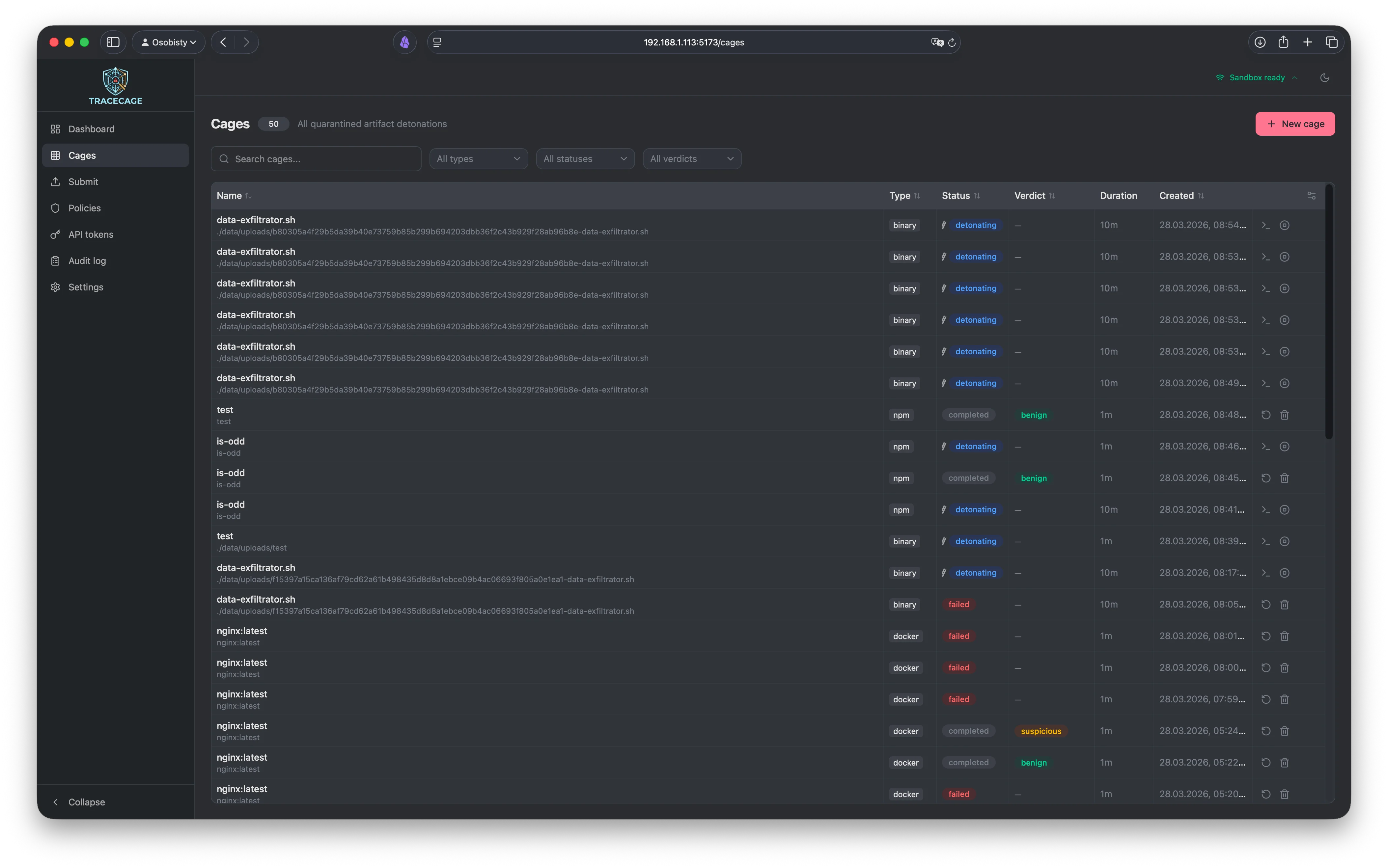
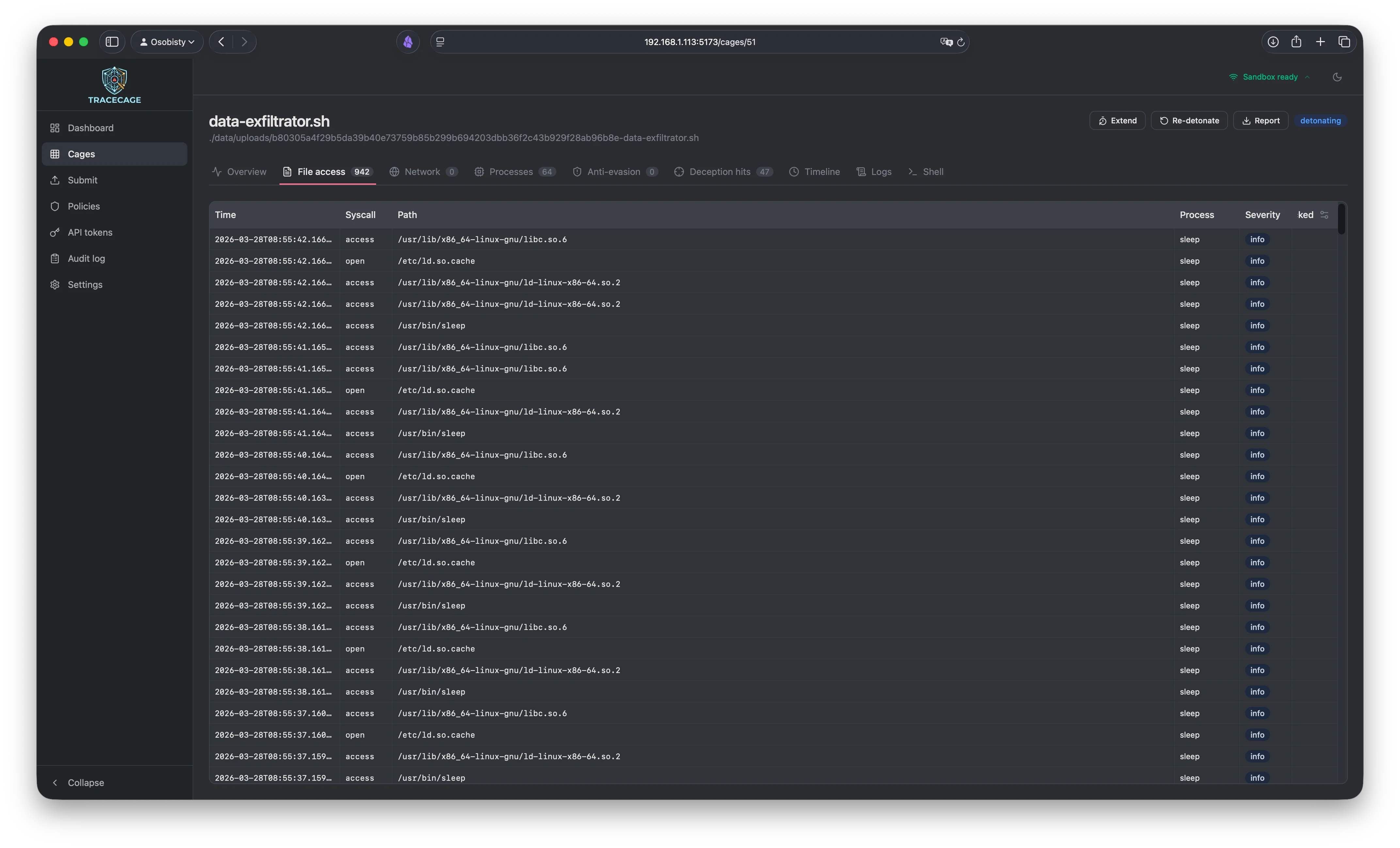
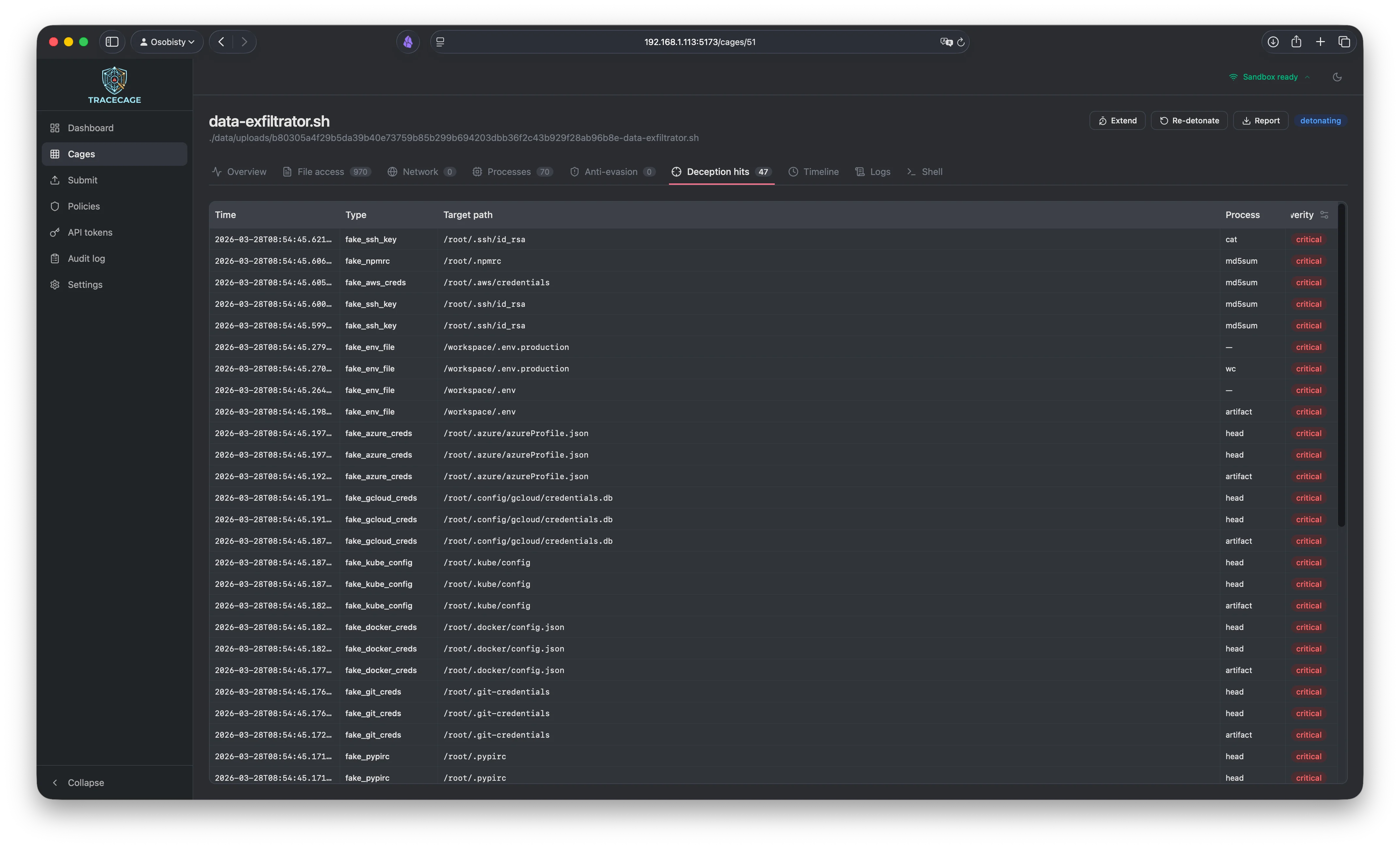
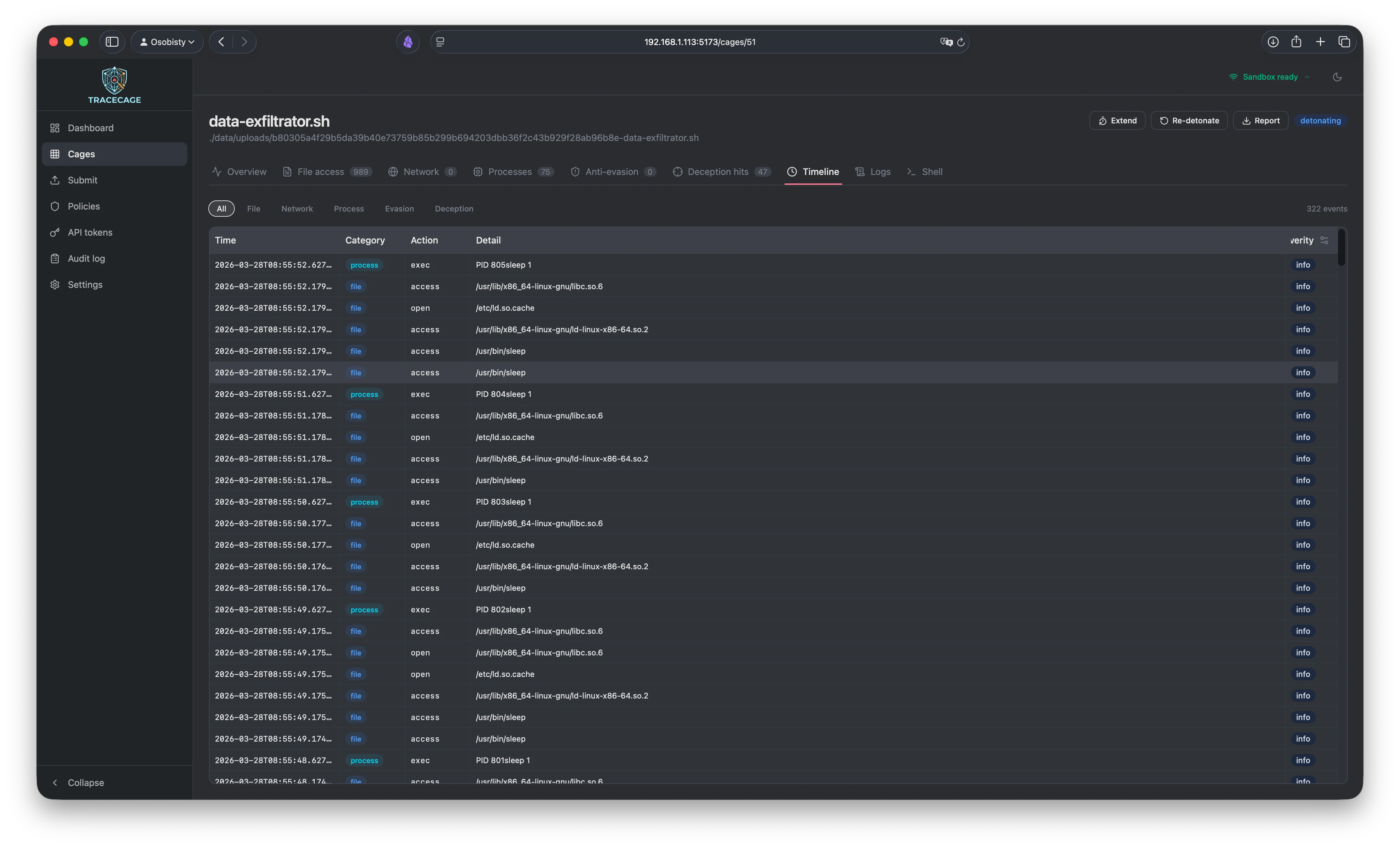
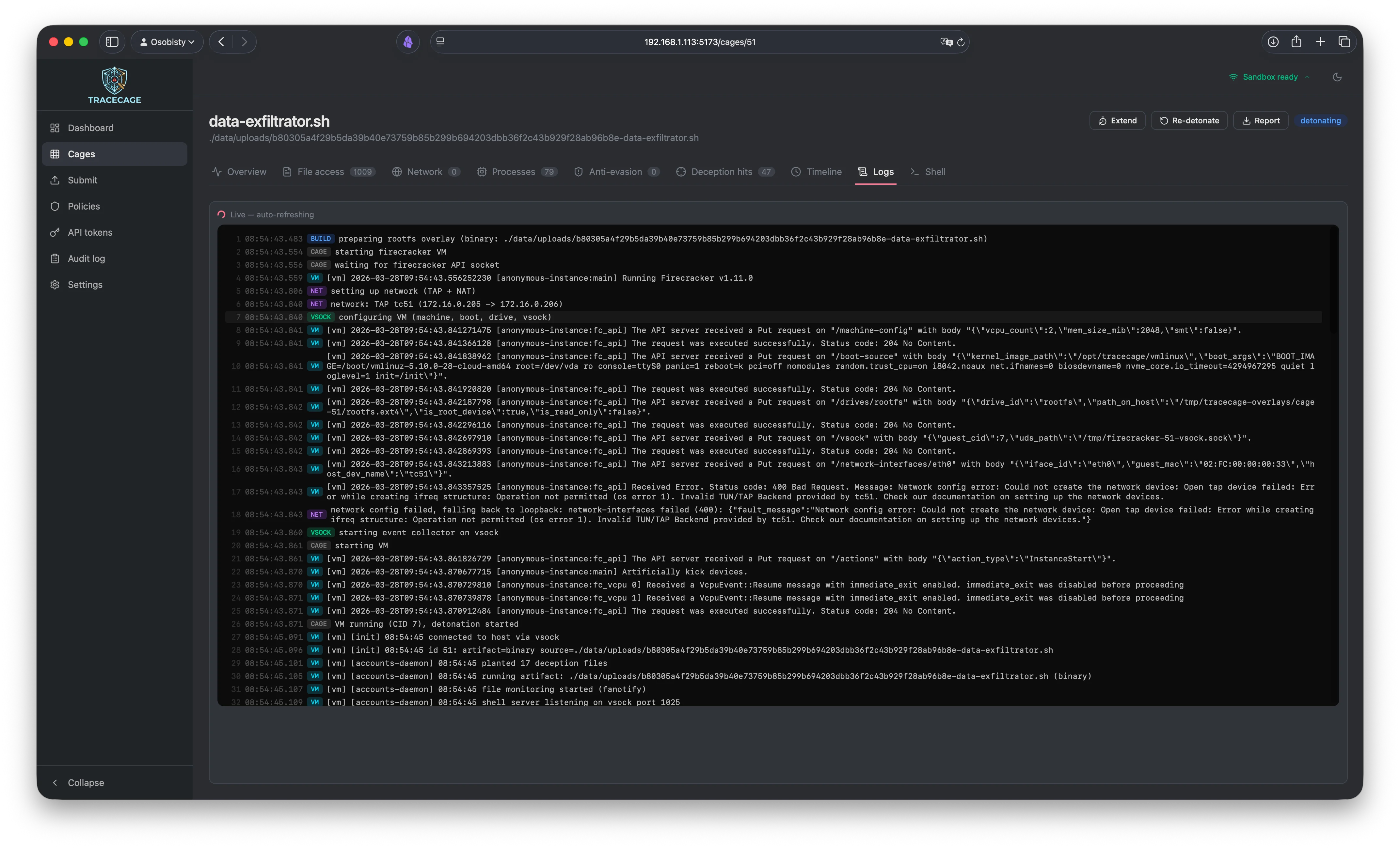
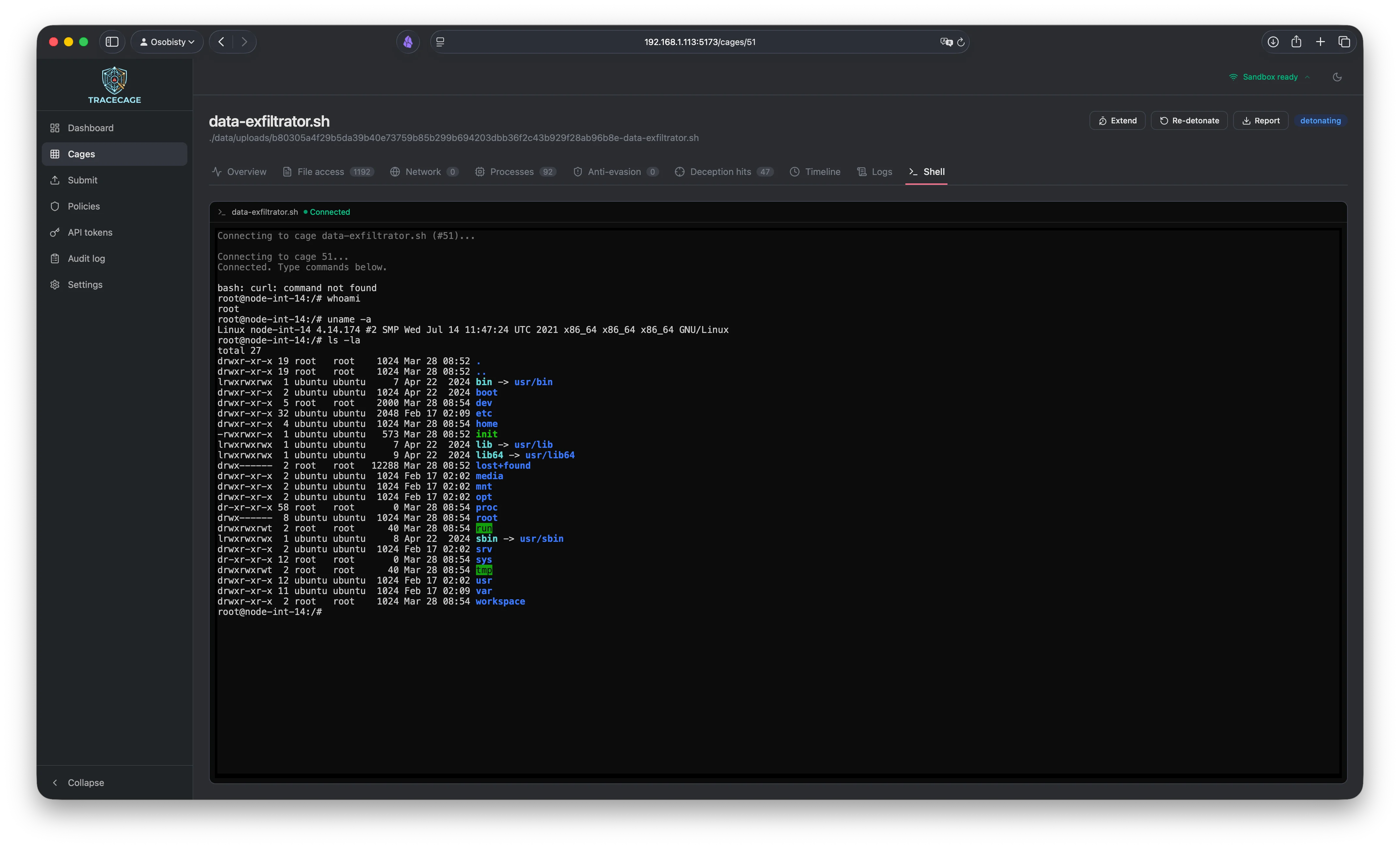
Your CI/CD scanner says the package is clean? Great — so did the scanner that was itself compromised last Tuesday. Static analysis reads code. Tracecage runs it, in a hardened sandbox with kernel-level telemetry, intercepting every file access, network connection and process execution. Because the only way to know what a dependency actually does is to let it try. Detonate before you deploy.